In the world of digital investigations, mobile forensics has become an essential skill for forensic investigators.
Whether you are new to the field or an experienced investigator, it is vital to have a solid foundation in the basics of mobile forensics.
With a comprehensive understanding of the different types of mobile data, legal considerations, and the mobile forensics process, you can conduct successful investigations and provide valuable insights.
Key Takeaways:
- Mobile forensics is an essential skill for forensic investigators to stay up-to-date with emerging technology.
- A comprehensive understanding of the basics of mobile forensics allows for successful investigations and valuable insights.
What is Mobile Forensics?
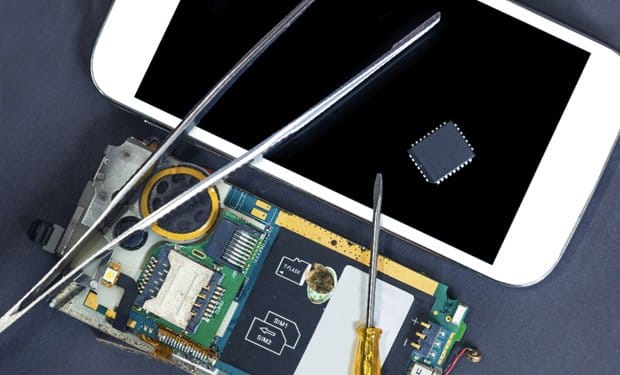
Mobile forensics is a digital investigation technique used to extract and analyze data from mobile devices such as smartphones and tablets.
With the widespread use of mobile devices, mobile forensics has become increasingly important in law enforcement, corporate investigations, and other types of digital investigations.
The process of mobile forensics involves accessing and recovering data stored on mobile devices, including call logs, text messages, emails, photos, videos, and app data.
The extracted data can be used as evidence in legal proceedings or to gain insight into a subject’s activities.
What does Mobile Forensics Encompass?
Mobile forensics includes various techniques and methods used to extract data from mobile devices. This can include:
- Physical and logical acquisition of data from the device
- Analysis of the acquired data using specialized software tools
- Recovery of deleted or hidden data from the device
- Extraction of data from cloud services and social media accounts
- Interpretation of the extracted data to identify user activities and behavior
Overall, mobile forensics plays a critical role in modern digital investigations, allowing investigators to gain access to and analyze information from mobile devices that could be crucial to solving cases.
Types of Mobile Data
During a mobile forensics investigation, a wide range of data can be extracted from the device. This section will delve into the different types of data that forensic investigators commonly encounter.
Call Logs
Call logs are records of all incoming and outgoing calls made on the device. These logs contain details such as the date and time of the call, the phone number, and the duration of the call. Call logs can be useful in establishing communication patterns between individuals.
Text Messages
Text messages are another important source of evidence in mobile forensics investigations. These messages can be retrieved from the device’s memory and examined for content, date and time stamps, and sender and recipient information. Text message analysis can be particularly useful in cases where individuals are suspected of illegal activities.
Emails
Emails are also a common source of evidence in mobile forensics investigations. They can reveal information about the device user’s contacts, professional activities, and personal interests. Email attachments may contain additional evidence, such as photos or documents that could be relevant to the investigation.
Images and Videos
Images and videos captured on the device can provide valuable evidence in mobile forensics investigations. These files may contain metadata such as location, date, and time stamps, which can be used to establish the device user’s whereabouts at a specific point in time.
App Data
Forensic investigators may also examine the data stored by specific apps on the device. This can include data such as user profiles, chat histories, and search activity. App data can be particularly useful in investigations related to social media and instant messaging apps.
Internet History
The device’s internet history can provide valuable insights into the user’s online activities. This includes their browsing history, search queries, and download history.
Overall, mobile devices contain a vast amount of data that can be relevant to forensic investigations. Understanding the types of data that can be extracted is a critical first step in conducting a successful mobile forensics investigation.
Legal Considerations in Mobile Forensics
When conducting mobile forensics investigations, it is crucial to consider the legal aspects of the process. In many cases, mobile devices contain sensitive and personal information, so it is important to adhere to laws and regulations related to privacy, data acquisition, and data retention.
Privacy Laws
It is essential to obtain proper legal authorization before conducting any mobile forensics investigation. The Fourth Amendment of the United States Constitution protects individuals from unreasonable searches and seizures. To safeguard privacy rights, investigators should adhere to local laws and regulations for obtaining search warrants or subpoenas before accessing mobile devices.
Data Acquisition and Retention Laws
Mobile forensic investigators must also adhere to data acquisition and retention laws. Different data types may have different requirements for acquisition and retention. For example, some types of data may require a court order to access or acquire, while others may require proper consent or notification before collection.
| Data Type | Legal Requirements |
|---|---|
| Text Messages | May require a court order to obtain |
| Photos and Videos | May require proper consent or notification before collection |
| Call Logs | May require a court order to obtain |
| GPS Location Data | May require proper consent or notification before collection |
Chain of Custody
Establishing and maintaining an unbroken chain of custody is crucial when conducting mobile forensic investigations. This involves documenting every person who handled the evidence, and ensuring that the evidence is protected and preserved throughout the investigation. Failure to comply with chain of custody requirements can lead to evidence being excluded in court.
By adhering to legal considerations when conducting mobile forensic investigations, we can ensure that the data collected is legally obtained, and that privacy rights are protected.
Mobile Forensics Process
Once we have all the necessary tools, the next step in mobile forensics is to follow a structured process, which typically involves the following steps:
- Preparation: In this initial stage, we need to ensure that we have the right tools and equipment to perform the investigation. We also need to identify the type of device and understand its operating system and configuration.
- Evidence Acquisition: This stage involves the physical or logical extraction of data from the mobile device. Physical extraction is the collection of data directly from the device’s memory, while logical extraction is the copying of data from the device’s file system.
- Data Analysis: In this stage, we analyze the data that we have acquired to identify relevant information that can help us in our investigation. This may involve using specialized software to search for specific keywords, deciphering encrypted data, or correlating data from different sources.
- Reporting: Finally, we need to present our findings in a clear and concise report that can be easily understood by non-technical stakeholders. The report should include a summary of the investigation, details of the data collected, and an analysis of the evidence.
Following this process ensures that our investigations are conducted in a methodical and repeatable manner, which is important when presenting evidence in a court of law. It also helps us to avoid missing critical pieces of evidence and ensures that our findings are reliable and accurate.
Tools and Techniques for Mobile Forensics
When it comes to mobile forensics, having the right tools and techniques can make all the difference. In this section, we’ll explore some of the most popular software and hardware solutions available in the market.
Tools for Mobile Forensics
There are many tools available for mobile forensics, each with its own strengths and weaknesses. Here are some of the most commonly used:
| Name | Description |
|---|---|
| Cellebrite | Cellebrite is a popular hardware solution used for extracting data from mobile devices. It can extract data from a variety of devices, including iPhones, Androids, and BlackBerries. |
| Magnet AXIOM | Magnet AXIOM is a software solution used for analyzing digital evidence from mobile devices. It can extract data from a variety of apps and devices, including GPS data, social media records, and chat histories. |
| Oxygen Forensic Detective | Oxygen Forensic Detective is another software solution used for extracting data from mobile devices. It has a user-friendly interface and can extract data from a variety of sources, including deleted files and app data. |
Techniques for Mobile Forensics
In addition to using the right tools, there are a number of techniques that forensic investigators can use to maximize their success in mobile forensics. Here are some of the most commonly used:
- Chip-off analysis: This technique involves physically removing the memory chip from a device and extracting data directly from the chip.
- JTAG analysis: JTAG (Joint Test Action Group) is a technique used for accessing the data on a mobile device’s printed circuit board (PCB).
- Bootloader unlocking: This technique involves unlocking the bootloader of a mobile device to gain access to its file system.
When using these techniques, it’s important to follow best practices and ensure that the integrity of the evidence is maintained throughout the investigation.
Challenges in Mobile Forensics
As with any forensic investigation, mobile forensics poses a number of challenges that investigators must be prepared to face. In this section, we will discuss some of the most common challenges encountered in mobile forensics and offer our insights on how to overcome them.
Device Encryption
One of the biggest challenges in mobile forensics is dealing with device encryption. Many modern mobile devices are equipped with encryption features that make it difficult, if not impossible, to access the device’s data without the correct credentials. This means that investigators must find ways to bypass or disable these security measures in order to extract the data they need.
Solution: There are a number of techniques that can be used to bypass device encryption, including the use of specialized software or hardware tools. In some cases, it may also be possible to gain access to a device by exploiting security vulnerabilities or weaknesses in the device’s software.
Locked Devices
Another common challenge in mobile forensics is dealing with locked devices. This can include devices that are password-protected, as well as devices that have been locked remotely by an administrator or parental control software. Locked devices can prevent investigators from accessing the device’s data, making it difficult to conduct a thorough investigation.
Solution: Depending on the circumstances, there are several ways to gain access to a locked device. One possible option is to obtain the device’s password or passcode from the device owner or other authorized party. In other cases, it may be necessary to use specialized software or hardware tools to bypass the device’s lock screen.
App-Specific Security Measures
Many mobile apps are equipped with security features that are designed to protect the user’s data from unauthorized access. These features can include password protection, encryption, and other security measures that can make it difficult for investigators to extract data from the app.
Solution: In order to overcome app-specific security measures, investigators must be familiar with the different types of security mechanisms used by different apps. They must also be able to work with specialized tools and techniques that are designed to extract data from individual apps.
By understanding and addressing these challenges, forensic investigators can conduct successful mobile investigations and extract valuable data from mobile devices.
Mobile Forensics Best Practices
When it comes to mobile forensics, there are certain best practices that should always be followed to ensure the preservation and accuracy of evidence. Here are some key tips to keep in mind:
- Document Everything: It’s crucial to document every step of the investigation process, from the initial setup to the final reporting. This documentation can be used to support your findings and conclusions in court.
- Preserve Evidence: It’s important to use forensically sound methods to extract, preserve, and analyze evidence. This includes maintaining the original source media and creating forensic images of the device(s) in question.
- Maintain Chain of Custody: It’s vital to maintain an unbroken chain of custody for all evidence collected during the investigation. This means documenting who had access to the evidence, when they had access, and what was done with it.
- Stay Up-to-Date: Mobile devices and the software they run are constantly evolving. It’s important to stay up-to-date with the latest methods and tools for mobile forensics to ensure that evidence is extracted and analyzed correctly.
- Train and Certify: Properly trained and certified forensic investigators are crucial to the success of any mobile forensics investigation. Be sure to seek out reputable training programs and certifications to ensure that you have the necessary skills and knowledge.
- Be Thorough: Remember, every detail counts in a forensic investigation. Make sure to conduct a thorough analysis of all evidence and document all findings, even if they seem insignificant.
By following these best practices, you can ensure that your mobile forensics investigations are conducted reliably and professionally, and that you are always prepared to present your findings in court.
Emerging Trends in Mobile Forensics
As technology continues to evolve at a rapid pace, the field of mobile forensics must keep up with the latest trends and advancements to stay relevant. Here are some of the emerging trends in mobile forensics:
- Cloud Forensics: With the increasing use of cloud storage, forensic investigators must be able to extract data from cloud-based services, such as iCloud, Google Drive, and Dropbox. This requires a thorough understanding of cloud computing platforms and navigating complex storage architectures.
- Social Media Forensics: Social media platforms have become a primary source of evidence in digital investigations. Forensic investigators must be able to extract data from these platforms, including private messages, posts, and comments, while also considering the legal and ethical implications of doing so.
- Internet of Things (IoT) Forensics: As more and more devices become connected to the Internet, forensic investigators must be able to extract data from a variety of IoT devices, such as smart home appliances, wearables, and medical devices. This requires a deep understanding of how these devices operate and how to extract data from them.
- Mobile Malware Analysis: With the rise of mobile malware, forensic investigators must be able to analyze and identify malicious software on mobile devices. This requires a thorough understanding of mobile operating systems and the ability to analyze code and identify vulnerabilities.
- Artificial Intelligence (AI) in Forensics: AI is beginning to play a significant role in digital investigations, including mobile forensics. Forensic investigators must be able to understand and utilize AI technologies to improve efficiency and accuracy in data analysis.
As these trends continue to shape the field of mobile forensics, it is essential for forensic investigators to stay up-to-date with the latest advancements and technologies.
Training and Certification in Mobile Forensics
At our organization, we understand the importance of proper training and certification for those working in mobile forensics. With the constantly evolving nature of technology and the legal landscape, it is crucial for investigators to stay up-to-date with the latest techniques and best practices.
We recommend seeking out reputable training programs that offer hands-on experience and a comprehensive curriculum. Some popular options include the SANS Institute, the International Association of Computer Investigative Specialists (IACIS), and the National White Collar Crime Center (NW3C).
In addition to training, certification can demonstrate a level of expertise and professionalism in the field. Some certifications to consider include the Certified Forensic Computer Examiner (CFCE) from IACIS, the Certified Mobile Forensic Examiner (CMFE) from the High Tech Crime Network (HTCN), and the Certified Mobile Examiner (CME) from the Digital Forensic Certification Board (DFCB).
| Training Programs | Certifications |
|---|---|
| SANS Institute | Certified Forensic Computer Examiner (CFCE) |
| International Association of Computer Investigative Specialists (IACIS) | Certified Mobile Forensic Examiner (CMFE) |
| National White Collar Crime Center (NW3C) | Certified Mobile Examiner (CME) |
Investing in proper training and certification not only benefits the individual investigator, but also contributes to the overall integrity and credibility of the field of mobile forensics.
Basics of Mobile Forensics – Final Thoughts
We hope this comprehensive guide has helped you gain a better understanding of the basics of mobile forensics. As mobile devices continue to play a critical role in our personal and professional lives, it is essential to have a solid understanding of how to conduct digital investigations involving these devices.
From understanding the different types of mobile data that can be extracted during investigations to following best practices for evidence preservation and documentation, mobile forensics requires a careful and methodical approach.
As technology continues to evolve rapidly, it is also important to stay up to date on emerging trends in mobile forensics, including cloud forensics and social media forensics. Ongoing training and certification can help ensure that forensic investigators have the knowledge and skills necessary to effectively conduct mobile investigations.
Thank you for reading our guide to the basics of mobile forensics. We encourage you to continue learning and exploring this critical area of digital investigations.
Basics of Mobile Forensics FAQs
What is mobile forensics?
Mobile forensics is extracting and analyzing data from mobile devices for digital investigations.
What types of data can be extracted from mobile devices?
Mobile devices can contain various data types, including call logs, text messages, emails, images, videos, app data, GPS information, and more.
What legal considerations should be taken into account in mobile forensics?
Forensic investigators need to consider laws and regulations related to privacy, data acquisition, and data retention when conducting mobile forensics.
What is the mobile forensics process?
The mobile forensics process consists of several steps, including initial setup, evidence acquisition, data analysis, and reporting.
What tools and techniques are used in mobile forensics?
There are various software and hardware solutions available for mobile forensics, including tools for data extraction, analysis, and decryption techniques.
What are the common challenges in mobile forensics?
Forensic investigators often face challenges such as device encryption, locked devices, and app-specific security measures in mobile forensics.
What are the best practices for mobile forensics?
Best practices in mobile forensics include evidence preservation, proper documentation, maintaining a chain of custody, and following industry standards.
What are the emerging trends in mobile forensics?
Emerging trends in mobile forensics include cloud forensics, social media forensics, and the impact of emerging technologies on mobile investigations.
Is training and certification important in mobile forensics?
Yes, training and certification play a crucial role in ensuring the expertise and credibility of forensic investigators in mobile forensics.